Hackers & Tech Stuff
Hacks and exploits and how to prevent them and crypto tech details.
Gas
On the Ethereum network, “gas” refers to the unit that is used to measure the amount of computational effort required to execute a transaction or …
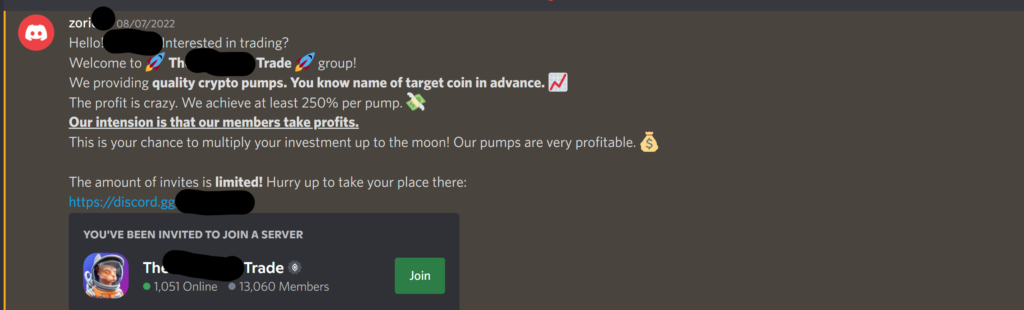
Pump ‘n Dump
A scheme to watch out for is the Pump and Dump scheme. This is where a group tries to get their users to buy a …
Bridge
What are Crypto Bridges? There are many different crypto tokens and most exist on their own Blockchains. It works exactly as it sounds: a bridge …
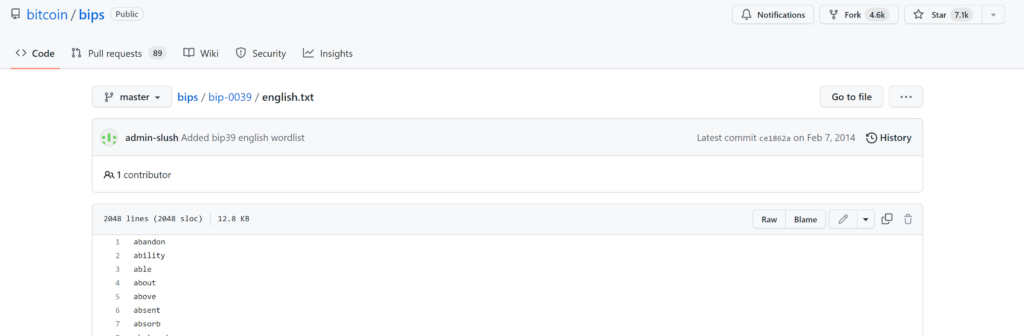
Seed Phrase
A Seed Phrase is basically the Master Key to your Crypto. It should therefore be guarded as such! Hackers and scammers want it as they …
Rug
A rug pull is when someone pulls whatever firm base you are standing on from underneath you, causing you to fall and crash. Though the …
Flash Loan Attack
Flash Loan Attacks are a type of DeFi attack where a cyber thief takes out a Flash Loan from a lending protocol and uses it …
Flash Loan
A flash loan is type of uncollateralized lending that has become popular across a number of decentralized finance (DeFi) protocols based on the Ethereum network. …
ERC
ERC or Ethereum Request for Comments are technical documents utilized by Ethereum smart contract developers. The documents define rules that are required to be followed …
Dusting Attack
A dusting attack is an attack in which malicious actors attempt to break the privacy of cryptocurrency (Bitcoin) users. This attack is a relatively new …
DDoS
A Distributed Denial of Service (DDoS) attack occurs when several compromised computer systems simultaneously attack a target machine, resulting in a denial of service for …
DOS
A Denial-of-Service (DoS) attack is a type of attack that is intended to cripple or shut down a machine or network. A DoS attack makes …
DeFi Insurance
Composability Risk
Composability Risk is the (additional and often exponential) risk resulting in stacking DeFi protocols. DeFi apps are highly composable since they can work easily with …
Composability
CDP
A collateralized debt position or CDP is held by locking collateral in smart contracts to generate stablecoins. MakerDAO was the first project that introduced CDPs. …
Censorship Resistance
Censorship resistance refers to the idea that no party can prevent anyone from participating in a given platform or network. Bitcoin was often used as …
Brute Force Attack
A brute force attack attempts to crack a password or key through automated trial and error. This is one of the most well-known and simplest …
$5 wrench attack
The $5 dollar wrench attack (5DWA) is a way of saying that criminals might use physical violence in order to steal your crypto funds. It …
2FA
2FA is short for Two-Factor Authentication. This is a security measure that lowers the chance of your account being hacked and/or abused. The first factor …
Not your keys, not your coins
Only the person that holds the secret key to a crypto wallet actually controls the crypto assets in it. In the case of a CEX, …
AABBC
The Armor Alliance Bug Bounty Challenge or AABBC was a revolutionary program. ease.org (then Armor) started this program early 2021 to stress the importance of …
Black Hat
A black hat is a type of hacker. It is a person who attempts to find computer security vulnerabilities and exploits them for personal financial …
Atomic swaps
Atomic swaps are automatic exchanges of cryptocurrency between two parties on two different blockchains without having to go through a centralized intermediary. The biggest advantage …
Cartels
This 51% attack is an issue for consensus models. A few nodes from the entire network take care of the overall governance. These delegates could …
Takeover attack
In this type of 51% attack, a malicious smart contract tricks the miners to lock up their money and mines a certain amount of blocks …
Goldfinger attack
In this 51% attack, an entity with an enormous amount of wealth buys a huge amount of ASICs and GPUs to corner the market when …
Dominating entity
Dominating entity This is the most common form of a 51% attack. In this attack, an entity gains more than 51% of the overall network …
51% attack
A 51% attack is a type of attack on a blockchain network in which an individual or group of individuals control more than 51% of …
Doxxing
Doxxing (or doxing) is the publication of personal details of a previously anonymous person. “The team is fully doxxed” means that there are no “anon” …
DEX
A peer-to-peer exchange that allows buyers and sellers to trade cryptocurrency directly with each other, without the need for an intermediary. This is the opposite …
CEX
Centralized exchanges (CEXs) are a type of cryptocurrency exchange that a company owns and operates in a centralized manner. Examples: Coinbase, Binance. Advantages of a …
Exploit
An exploit is a piece of code, data, or a sequence of commands that takes advantage of a bug or vulnerability in an application, protocol, …
Bug Bounty
A bug bounty or bug bounty program is a reward for finding and reporting a bug in a particular software product. The bounty programs attract …
Audit
Auditing refers to a project using a professional third party to evaluate the soundness of its code and hunt for potential weak points.
Arbitrage
Arbitrage is the practice of quickly buying and selling the same asset in different markets to take advantage of price differences between these markets. So, …